Architecture
Module Sandboxing: Elevating Security and Isolation Within App Ecosystem – Part 1
Piyush Jain, Mohsin Khan and Titas Datta11 October, 2023
Introduction
In the ever-evolving world of mobile app development, the need for heightened security, robust privacy measures, strict compliance adherence, and steadfast data isolation has become paramount. At the forefront of these concerns lies app sandboxing—a fundamental concept that fortifies application security by isolating it from the underlying operating system and other applications. However, while app sandboxing effectively isolates the applications, it falls short in providing the granular isolation that might be required for individual modules within a single application. In this first part of our three-part series, we introduce you to the concept of Module Sandboxing, a solution that addresses this limitation. Join us as we embark on a journey to unfold this approach and its significance in modern app development.
What is Module Sandboxing?
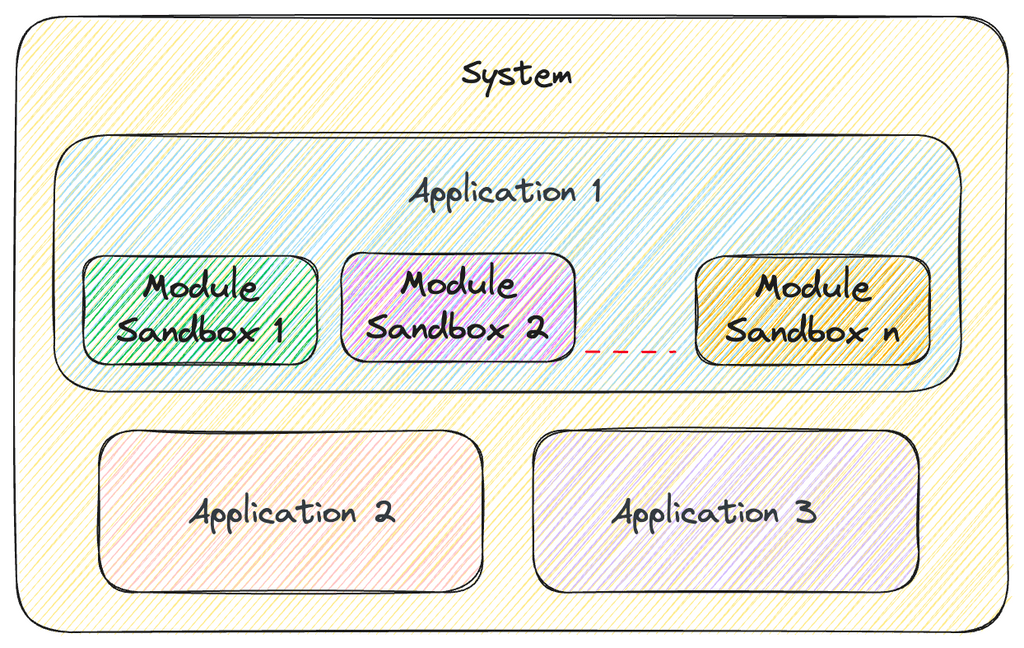
Module Sandboxing extends the principles of app sandboxing to the level of individual modules or components within an application, introducing a new layer of security and isolation.
In essence, the sandboxed modules are not only separated from the underlying operating system and other applications but are also isolated from each other and the containing app itself. This means that each module operates within its own confined environment, shielded from any interference or data exchange with other modules or the application itself.
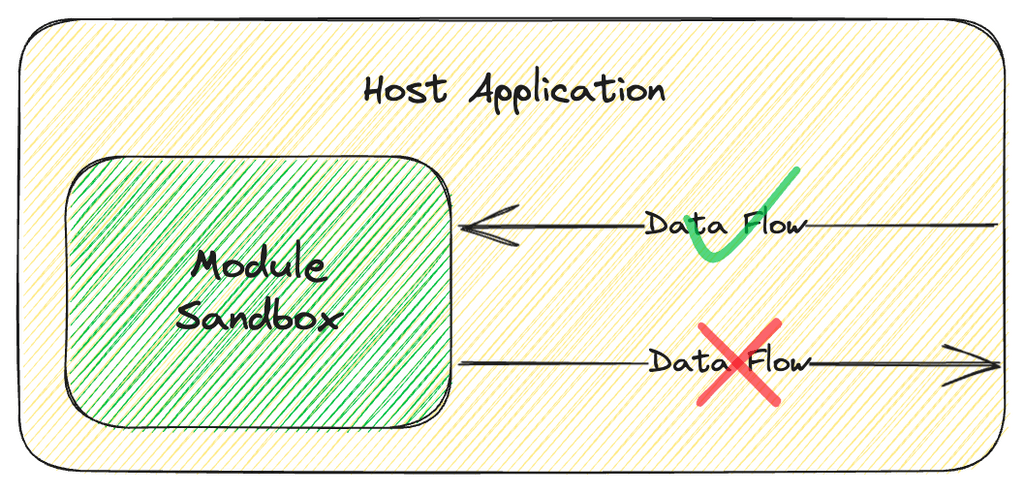
However, it’s crucial to note that while Module Sandboxing enforces data flow isolation of the sandbox module from the host app, we can choose to enable unidirectional data flow from the host app to the module as well. Much like app sandboxing permits certain system information to be accessed within an app, Module Sandboxing can facilitate a secure channel for data to flow into individual modules from the host application.
Key Features of Module Sandboxing
As the demand for sophisticated apps intensifies, so do concerns related to security, user privacy, compliance, and data isolation. Module sandboxing is a response to these demands. In this section, we delve into its critical aspects:
- Isolation: Each module operates within its own isolated environment or sandbox. This isolation prevents a malfunctioning or malicious module from affecting other parts of the software or compromising the system as a whole.
- Restricted Access: Module sandboxing enforces restrictions on what a module can access or modify within the application. It limits the module’s ability to interact with sensitive data, system resources, and other modules.
- Security Boundaries: Security boundaries are established around each module to prevent unauthorized access or communication. This helps prevent unintended data leaks or security breaches.
- Maintainability: Module sandboxing can improve the maintainability of a software system because each module is encapsulated and isolated. This makes it easier to update, replace, or remove modules without affecting the entire application.
- Compatibility: Module sandboxing can enhance compatibility by allowing the integration of third-party or user-generated modules without risking the stability or security of the core application.
- Compliance Adherence: In scenarios where modules or the containing app represent distinct regulated entities, Module Sandboxing plays a crucial role in compliance adherence by isolating and securing each module within its own compliance standards.
Benefits of Module Sandboxing
Here are the benefits of module sandboxing:
- Unparalleled Isolation: Sandboxed modules excel in creating a fortress of isolation. They operate autonomously, safeguarding user data from external threats and potential breaches.
- Controlled Ecosystem: Within the sandboxed environment, modules enjoy a controlled ecosystem. This autonomy ensures that any adverse impact remains contained within the module itself, preserving the user experience.
- Robust Security: Sandbox modules, by design, bolster app security. Their inherent isolation minimizes the risk of security vulnerabilities and unauthorized access.
- Enhanced Privacy: The privacy of user data is a paramount concern in today’s digital landscape. Module sandboxing enhances user privacy by limiting the reach of modules, preventing unwarranted data access, and ensuring that sensitive information remains confidential.
In conclusion, Module Sandboxing is an extension to App Sandboxing, offering heightened security, precise data isolation, and granular control over different modules within an application. By encapsulating and isolating individual modules, it enhances maintainability, compatibility, and compliance adherence while fortifying app security and user privacy.
Stay tuned for the upcoming segments of this series, where we will delve into the details of Module Sandboxing implementation.